Since the release of Cybersecurity Maturity Model Certification (CMMC) version 0.4 in late 2019, the program has been in a constantly evolving state. On November 5th, after a prolonged internal review, the Department of Defense (DoD) communicated its most significant changes to date with CMMC 2.0.
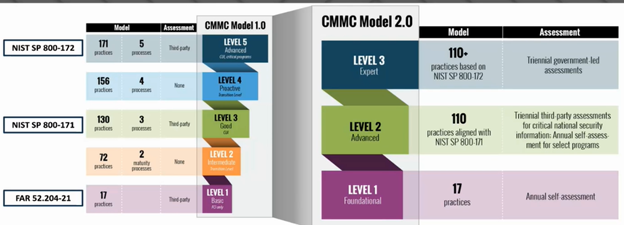
Prior to the announcement on November 5th, CMMC 1.0 (as it is now referred to) included 5 levels. Level 1 was designed to protect Federal Contract Information (FCI) and support basic cyber-hygiene by utilizing 17 security practices. Level 3 required 130 practices to protect Controlled Unclassified Information (CUI) and provide the contractor with good cyber-hygiene. Level 5 sought to reduce the risk of advanced cyber threats and be used for contracts dealing with highly sensitive defense information. It required contractors to achieve 171 practices. Levels 2 and 4 were envisioned as steppingstones for companies to grow their cyber protections to meet the level 3 and 5 requirements, which along with Level 1 would be certification levels. Under CMMC 1.0, every company seeking a certification, which would allow them to participate on a DoD contract, was required to be assessed and certified by a CMMC Third-Party Assessment Organization (C3PAO). A 100% passing score indicating all requirements had been fully implemented was required to achieve certification. However, this third-party assessment requirement was proving to be a challenge for both the assessors and the contractors. C3PAOs are limited in number and the time it would take to certify each company at their respective level was gaining more criticism as time passed.
Wait times to be certified was not the only criticism against CMMC 1.0. The DoD received over 850 public comments on Interim Rule 2019-D041 which led to the changes seen in CMMC 2.0. Three main changes were implemented revolving around certification levels, certification assessments, and the allowance of Plans of Actions and Milestones (POA&Ms).
1. The largest change is the restructuring of CMMC’s certification levels, going from 5 levels down to 3, effectively eliminating levels 2 and 4. Level 1, “Foundational” Requirements, will apply to most DIB contractors and require 17 basic cyber-hygiene practices, consistent with level 1 of CMMC 1.0. At Level 2, “Advanced” Requirements, implements 110 practices which aligns with the NIST SP 800-171 framework required under DFARS 252.204-7012. Level 3, “Expert” Requirements, are still being developed but is expected to require the 110 practices from level 2 as well as select practices from a subset of NIST SP 800-172, which focuses on advance persistent threats and sophisticated cybersecurity threats.
2. The second largest change relates to the third-party certification requirements. Contractors at level 1 and a subset of contractors at level 2 will be able to perform an annual self-assessment in lieu of a third-party assessment to show compliance. Level 2 contractors with access to “information critical to national security” will have to be assessed through a C3PAO every three years. All level 3 contractors will be reviewed through a government led assessment, assumed to be conducted by the DCMA Defense Industrial Base Cybersecurity Assessment Center, on a three-year basis.
3. Finally, POA&Ms, which were not allowed under CMMC 1.0, will be accepted for contractors who don’t meet certain controls to detail how and when they will achieve the missing requirements. If a contractor’s POA&M is sufficient they would still be eligible for procurements. More details will be released on this system especially based around what levels of certification POA&Ms would apply to. However, at this time it should be noted that while it has been communicated that POA&Ms will be accepted, the DoD’s intent is to specify a baseline number of requirements that must be achieved prior to contract award, in order to allow a remaining subset to be addressed in a POA&M within a clearly defined timeline. The DoD also intends to specify a small subset of requirements that cannot be on a POA&M in support of achieving a CMMC certification.
These changes are an attempt to directly address the concerns contractors had with CMMC, and to make certifying less of a financial and logistical burden. CMMC 2.0 is promising to reduce costs, especially for small and medium sized business. The streamlining of certification levels along with the ability to self-asses should reduce costs enough for small contractors to continue to seek out contracts with the DoD. The government is also planning on releasing a cost analysis for each level of certification to provide more clarity to contractors on how expensive certification will be. Contractors should also expect the government to be more flexible when reviewing certification assessments using POA&Ms. The timeline for these changes remains contractors’ biggest question. CMMC 1.0 requirements are being immediately suspended, and contractors will not see any CMMC requirements in new DoD solicitations. Currently, CMMC 2.0 is going through the rule making process outlined in part 32 and part 48 of the Code of Federal Regulations. The expectation is that the rule making process could take anywhere from 9-24 months. Until then, contractors must continue to follow the cybersecurity requirements contained in their contracts, primarily FAR 52.204-21, DFARS 252.204-7012, DFARS 252.204-7019, and DFARS 252.204-7020, and keep in mind that the Department of Justice is enhancing its capabilities to evaluate and enforce False Claims Act violations involving cybersecurity through its recent Civil Cyber-Fraud initiative.
Source: https://www.acq.osd.mil/cmmc/about-us.html
Chess Consulting has experience assisting DIB contractors of all sizes to understand how the requirements of the DFARS cyber clauses impact their organization. Our extensive experience assisting contractors with government contract compliance matters paired with a deep understanding of cybersecurity and information security practices allows us to provide our clients with a holistic approach to compliance. Contact a Chess professional today.
